Education
8 Cyber Security Protocols You Didn’t Know You Needed
Published
2 years agoon
By
techonpc
Cyber Security
You probably know that cybersecurity is important, but do you know what steps to take to make sure you’re staying safe? The majority of people are already adopting cybersecurity measures in some way, so that’s good news. The bad news is that there are still a lot of companies out there who aren’t taking basic precautions. So, let’s dive into what these practices entail, why they matter so much, and how you can implement them at your company.
DNS Protection
DNS protection is the practice of blocking access to your computer from any external DNS server. A DNS server is what directs your computer to the right website when you type in a URL, and it can also be controlled by hackers who want to redirect you to fake websites. If a hacker successfully takes over one or more of your organization’s DNS servers, they can use them to steal personal information from unsuspecting employees, steal company data, and even install botnets on your network.
Have a Disaster Management Plan
Create a recovery plan that will enable you to recover your data in case of an emergency. It should include details of how you can access your files as well as information about how long it takes you to make backups of important files and where they are stored. This will help ensure that if there is ever an attack on your network, the damage will be limited and fixable quickly without affecting the rest of your business operations too much.
A disaster management plan usually starts with creating off-site copies of data and having regular backups at a secure location. This can mitigate not only cyberattacks but physical emergencies as well such as tornadoes and floods.
Use a VPN
A VPN is a way to protect your data when you’re using the internet. If you’re accessing the internet through public Wi-Fi, it’s possible that someone else may be trying to listen in on your activity and steal information from you. A VPN makes it harder for people like this to find out what you’re doing online by encrypting all of the data that travels between your computer and the server of the VPN provider. This means that even if someone does intercept something, they’ll have no idea what it says because all of it will look like gibberish to them.
Use a Password Manager
A password manager is a type of digital assistant that helps you create, store and manage strong passwords across all your devices. A great password manager will keep track of all your passwords and let you access them from anywhere, without having to remember them or write them down.
Encrypt Your Data
Encrypted data is unreadable by anyone except those possessing special knowledge, usually referred to as a key. Data encryption is the process of encoding information to keep it secure in email, on servers, and anywhere stealthy hackers might try to access it. Using encryption software helps you protect more of your business data than ever before.
Turn on Two-Factor Authentication
Leveraging all the cybersecurity protocols at your fingertips is critical. One of the easiest for everyone to use is two-factor authentication. Two-factor authentication is an extra layer of security that you can add to your online accounts, such as your email and social media profiles.
With two-factor verification, when you try to log in from a new device or browser, the site will ask for both a password and a unique code that isn’t stored on the device where you’re trying to sign in. This means if someone gets hold of your password, they won’t be able to access your account unless they have access to another device with two-factor authentication enabled. This can protect you from phishing attacks and other malware issues that might try to steal your information.
Keep Your Computer in a Secure Location
It’s not smart to leave your laptop in your car. Instead, keep it in the office or at home unless you are using it. The more secure you can keep the computer, the more secure the data in it will be. This includes any data that the computer might have access to when it connects to your company network.
Create Cybersecurity Policies For All Staff
Create a password policy so that all employees follow guidelines for creating strong passwords with varying length combinations and complexity requirements when choosing their passwords for each account on their computer or smartphone device. Teach them good habits regularly so that they learn how to identify questionable emails and websites where threats often try to come in.
Follow Me

Unleashing the Power of the Office Accelerator: Maximizing Productivity and Efficiency in the Workplace with Office 365 Accelerator

Expanding Your Brand’s Digital Presence with Image Clipping Path

The Power of Data Cleansing in Improving Business Decisions
Trending
 Microsoft4 years ago
Microsoft4 years agoMicrosoft Office 2016 Torrent With Product Keys (Free Download)
 Torrent4 years ago
Torrent4 years agoLes 15 Meilleurs Sites De Téléchargement Direct De Films 2020

 Money3 years ago
Money3 years ago25 Ways To Make Money Online
 Torrent4 years ago
Torrent4 years agoFL Studio 12 Crack Télécharger la version complète fissurée 2020
 Education3 years ago
Education3 years agoSignificado Dos Emojis Usado no WhatsApp

 Technology4 years ago
Technology4 years agoAvantages d’acheter FL Studio 12

 Technology3 years ago
Technology3 years agoDESKRIPSI DAN MANFAAT KURSUS PELATIHAN COREL DRAW
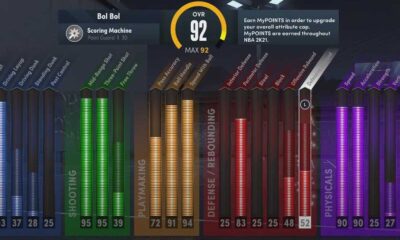
 Education3 years ago
Education3 years agoBest Steph Curry NBA 2K21 Build – How To Make Attribute, Badges and Animation On Steph Curry Build 2K21

You must be logged in to post a comment Login