Education
Supply Chain Trojans Are Forcing A Security Revolution
Published
1 year agoon
By
techonpc
Virus
Supply chain attacks are becoming increasingly aggressive thanks to large-scale and deeply complex campaigns that have completely overturned the last few decades of perimeter security thinking. Data protection security is facing increased risk from profiteering cybercriminals and malicious state actors alike. Virtual patch solutions seem to be one of the leading ways forward in battling weak links in the software supply chains.
The Growth of Supply Chain Attacks
The tail end of 2019 rocked the cybersecurity world. A completely-overlooked vulnerability had snuck its way onto the latest update of SolarWinds’ Orion platform. This is a solution used by companies around the globe for monitoring their IT systems. The attack was intensely sophisticated, with attackers slipping a trojan into the legitimate Orion update on SoalrWind’s own servers. This trojan-update was signed with a valid digital certificate, allowing for the first stage of the attack to slip through defenses completely unnoticed.
Once infiltrated, the attackers chose to steal and reuse credentials, moving laterally throughout an infected network. This legitimate backdoor access was then used to deliver a completely novel lightweight malware dropper. FireEye has since dubbed it TEARDROP. This malware dropper loads directly in memory, leaving no traces behind on the disk. TEARDROP was then used to deploy a customized version of Cobalt Strike’s BEACON payload. BEACON is an espionage tool that logs keystrokes, takes screenshots, and downloads all files onto an attacker-controlled command and control server.
SolarWinds’ customer base included the vast majority of the US Fortune 500; all branches of the US military, the Pentagon and the State Department. Alongside playing a critical role in national security, they also provided software for the top US accounting firms and hundreds of universities and colleges worldwide. It’s thought that the group responsible for this attack was affiliated with the Russian government.
Supply chain attacks represent the ultimate in espionage. It’s a possibility that the SolarWinds attack took direct inspiration from a similar attack in 2017. In this case, a supply-chain attack was unleashed by the established Advanced Persistent Threat (APT) group Winnti. The group broke into the infrastructure of NetSarang – a company that makes server management software – before distributing trojan-infected versions of the product for new customers. It’s thought that this process allowed them to further compromise the development infrastructure of Avast subsidiary CCleaner, which then allowed them to distribute malware to over 2.2 million users.
The Costs of Low Visibility
Supply chain attacks make incredibly alluring attacks, thanks to the sheer volume of victims possible through each attack. Companies are becoming increasingly vulnerable to these attacks, even while some continue to stubbornly ignore the issue at hand. Recent research from BlackBerry discovered that four out of five (80%) organizations have – within the last 12 months alone – been notified of a vulnerability or attack in their supply chain. This survey focused on IT decision makers throughout North America, the UK and Australia, with growing impacts measured for every attack. Over half of those notified then went on to experience operational disruption, intellectual property loss, and data loss.
One component of the growth in supply chain attacks is the industry’s increasing reliance on open source software. This presents a natural opportunity for illicit actors, as a dependence on open source is often coupled with a critical shortage of skilled employees and up-to-date resources. The implementation of open-source is also regularly hidden within third-party code, or buried within lines and lines of opaque application architecture. The visibility issue is rampant: it grossly undermines the other security goals of an organization, and is one reason why security experts are warning of a 430% year-on-year increase in supply chain attacks.
The same warning cited the fact that in 2019, over 10% of Java OSS downloads were suffering from at least one open source vulnerability. The report also found that these flaws were being regularly exploited within three days of their public disclosure. The issue of chronic open source vulnerabilities would be a niche issue, if it weren’t for the fact that open source components make up 90% of today’s applications. This is why the next generation of cyberattacks will continue to shift upstream, where attackers can focus their efforts on infecting a single open source component, before strategically exploiting its downstream victims.
Patching Up The Weak Links
The traditional answer to security weak links within web apps has been the Web Application Firewall (WAF). However, the recent widespread adoption of agile and DevOps practices has helped push modern web applications and APIs past the capabilities of the traditional WAF. Web apps and APIs are in a continuous state of flux; the continuous tuning and policy creation that the WAF demands can turn this tool into more of a security liability.
Instead, the software supply chain crisis now demands tools such as the Web Application and API Protection (WAAP) service. This solution inspects all requests reaching the web app and APIs before they reach the endpoint or app. A broad WAAP service includes a number of key capabilities, including Runtime Application Self-Protection (RASP). This functionality sits within the application runtime domain itself, monitoring its normal behaviors and activities. If anything seems out of place, RASP can either alert the DevSecOp team, or automatically terminate the suspect behavior. The other key aspect is a next-gen WAF. Similar to its traditional cousin, this protects and monitors the web app from the application layer. However, the next-gen aspect describes the fact that this tool is loaded with artificial intelligence that focuses on behavioral analysis. No longer is the team required to manually update every single policy; the behavior recognition software allows for injection attacks, privilege escalation and other malicious actions to be blocked, without relying on known attack patterns and signatures.
With a suitable hand of anti- supply chain attack tools, it is possible to nip the problem in the bud – before it hits your or your clients’ customers.
Follow Me

Unleashing the Power of the Office Accelerator: Maximizing Productivity and Efficiency in the Workplace with Office 365 Accelerator

Unlocking the Hidden Potential of Your Website: Strategies for Growth

From AI to VR: How Cutting-Edge Tech Is Reshaping Personal Injury Law in Chicago
Trending
 Microsoft4 years ago
Microsoft4 years agoMicrosoft Office 2016 Torrent With Product Keys (Free Download)
 Torrent4 years ago
Torrent4 years agoLes 15 Meilleurs Sites De Téléchargement Direct De Films 2020

 Money4 years ago
Money4 years ago25 Ways To Make Money Online
 Torrent4 years ago
Torrent4 years agoFL Studio 12 Crack Télécharger la version complète fissurée 2020
 Education3 years ago
Education3 years agoSignificado Dos Emojis Usado no WhatsApp

 Technology4 years ago
Technology4 years agoAvantages d’acheter FL Studio 12

 Technology4 years ago
Technology4 years agoDESKRIPSI DAN MANFAAT KURSUS PELATIHAN COREL DRAW
 Education3 years ago
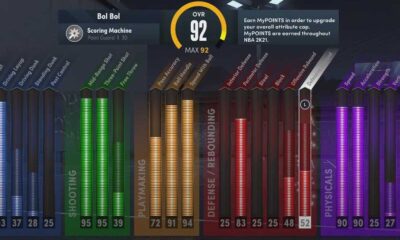
Education3 years agoBest Steph Curry NBA 2K21 Build – How To Make Attribute, Badges and Animation On Steph Curry Build 2K21

You must be logged in to post a comment Login