Technology
The Six Greatest Goals of PCI Compliance
Published
3 years agoon
By
techonpc
PCI Compliance
Payment Card Industry or PCI compliance is critical to your business’ success. The PCI standards exist to confirm how well people are handling credit card data. Those who understand how they can manage credit card payments and keep them accurate will ensure everyone’s data stays safe and will not be lost for any purpose.
Anyone who wants to accept credit card payments must meet PCI compliance standards. You can reach that point if you meet the six general goals of reaching PCI standards for whatever work plans you wish to handle.
1. Keep your network secure.
The first point to follow entails keeping your network safe. You can secure your network by installing a firewall to keep cardholder data in check. A hardware-based firewall works for external connections, while an internal firewall does well for interior links between people in your business.
PCI rules also state people should not use the default passwords that come with their network security systems. All parties should have unique passwords for operation. The store can also include policies where they must change passwords every few weeks or months. Each person who has access to your system must also have unique passwords without repeating the same details when handling their access points.
Failing to keep a network protected will result in outside parties entering the space without permission. The network will struggle to work as well as you wish, plus your customers’ data may be exposed if someone finds it soon enough.
2. Keep cardholder data safe.
Your customers will entrust you with their credit card data when they make purchases with you. You must return the favor by protecting their cardholder data. You can use restricted server access for cardholder databases, plus you can use bank-grade encryption for all transactions people complete. The encryption includes obscuring transaction signals on a public network while being selective over which ports will accept data.
You must also avoid storing sensitive pieces of data in your database. These include CVV numbers, PINs for access, and any unique numerical identifiers like a Social Security Number, Medicare number, or anything else someone holds. These numbers will confirm someone’s identity at the start, but they will be discarded afterward. You can save the other card details, but these sensitive points cannot appear in your report.
Keeping those details out of the way is necessary for everyone’s safety. If a person tries to steal card data or illegally access it, that person won’t have access to the CVVs or some other details. Anyone who steals the data will not have everything in hand, significantly reducing the risk of peoples’ data being stolen and used for other purposes outside what regularly works.
3. Prevent viruses and other external threats from entering your business system.
The next part of PCI compliance entails keeping all security vulnerabilities under control. Antivirus programs can assist you in protecting against viruses, malware, and other outside threats. All antivirus programs you use must be updated and checked to ensure they stay functional. All applications and connection systems you utilize must also be effective while identifying and neutralizing outside threats as necessary.
Regular updates are necessary, as computer viruses and illegal programs are always evolving. You might find some new features that are very different from what you’re used to managing. You can request scheduled updates for all your systems as you see fit.
4. Limit access to your data.
The credit card processing data you collect must only be made available to those who have permission to handle that content. You can limit cardholder data access to a need-to-know basis, meaning it is only accessible when necessary for a payment.
You can also create unique identification numbers or names for each person who has access to the data. This point helps you monitor and identify who is using something at a time. It traces details back as necessary, plus it holds people accountable for what they are doing with their work.
Another effort to follow involves producing permissions for each employee. You can set permissions for which databases someone can access, what information someone can collect, and other points. You can use as many permissions as you wish, but they must be spread well between all your employees.
5. Test all security features you utilize.
A merchant services provider can help you review all the security features you’re using in your workplace. Regular PCI audits may review what you are doing and find potential issues you need to resolve. Routine tests from online merchant services providers can be done in the background or when you’re out of the office.
An independent auditor can review the work and see what needs fixing. You may be subject to a PCI compliance fee to cover the cost of a review, but it can be worthwhile when you consider the potential losses that might occur from not being compliant. You can prevent problems surrounding legal issues from peoples’ data being stolen, for example.
6. Produce a security policy everyone in the workplace can follow.
The last goal of PCI compliance is to ensure everyone follows a consistent security policy. You can produce a policy that covers everything from how people access data to what they should be doing with the content they handle. Everyone should be on the same page surrounding how data works and what people can do with this content. You can update the content as necessary, but the employees must be made aware of any new changes you complete.
All these points for credit card processing can be critical for your success in giving people a place where they can safely handle their transactions. PCI compliance is critical for ensuring your business stays secure and that people can trust what you provide. You don’t have to spend too much time trying to figure out what you should be doing when making your business compliant with all the PCI rules you need to manage.
Follow Me

Unleashing the Power of the Office Accelerator: Maximizing Productivity and Efficiency in the Workplace with Office 365 Accelerator

Unlocking the Hidden Potential of Your Website: Strategies for Growth

From AI to VR: How Cutting-Edge Tech Is Reshaping Personal Injury Law in Chicago
Trending
 Microsoft4 years ago
Microsoft4 years agoMicrosoft Office 2016 Torrent With Product Keys (Free Download)
 Torrent4 years ago
Torrent4 years agoLes 15 Meilleurs Sites De Téléchargement Direct De Films 2020

 Money4 years ago
Money4 years ago25 Ways To Make Money Online
 Torrent4 years ago
Torrent4 years agoFL Studio 12 Crack Télécharger la version complète fissurée 2020
 Education3 years ago
Education3 years agoSignificado Dos Emojis Usado no WhatsApp

 Technology4 years ago
Technology4 years agoAvantages d’acheter FL Studio 12

 Technology4 years ago
Technology4 years agoDESKRIPSI DAN MANFAAT KURSUS PELATIHAN COREL DRAW
 Education3 years ago
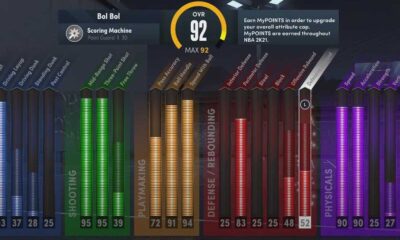
Education3 years agoBest Steph Curry NBA 2K21 Build – How To Make Attribute, Badges and Animation On Steph Curry Build 2K21

You must be logged in to post a comment Login