Education
Why Organizations Shall Focus on Cyber Recovery Automation and Data Security
Published
1 year agoon
By
techonpc
Data Security
As cyber security is a topic of increasing importance in the world of technology, companies are constantly being forced to protect themselves from malicious attacks and other threats. And the solutions come with compliance which is the name of the game for business continuity and disaster recovery programs. The world has become increasingly complex, and businesses need to operate in ways that meet both their internal processes as well as those established by external regulations. In times like today, when businesses cooperate and often share their clients’ data with third-party organizations, these laws and regulations are even more crucial.
In the article, we are talking about some major compliance regulations that mandate cloud solution service providers, organizations, and business owners to properly manage personal information regardless of the industry, and ensure the citizen’s rights are protected within SOC 2, GDPR, HIPAA, PCI DSS, FISMA, etc.
Organizations need to focus on cyber resilience
Besides focusing on data security, organizations should also be taking steps to improve their cyber resilience. Cyber resilience is the ability of an organization to withstand, recover from, and adapt in the face of cyberattacks. It’s not just about protecting data; it’s about protecting the entire application and infrastructure that supports business operations. For an organization’s cyber resilience plan to be effective, it must encompass all aspects of its environment–including cloud services such as Amazon Web Services (AWS) or Microsoft Azure Stack–as well as physical infrastructure like routers and switches that connect networks together at different levels within an enterprise network architecture (NIA).
As you evaluate your options, don’t expect a single solution to solve all your problems. It’s important to consider your specific needs and budget, as well as security requirements and availability requirements.
For example: If you’re looking for an automated backup solution that will allow you to recover from ransomware attacks within minutes, then a cloud-based service might be better than an on-premises appliance that takes hours or days. On the other hand, if cost is not an issue but speed matters most (like when recovering from some kind of malware attack), then an on-premises appliance may be worth considering over its cloud counterpart because it can provide faster recovery times by storing data locally rather than remotely in another location–and this means less latency between when an incident occurs and when IT staff members can start working on recovering data back up again!
The Cloud is a part of the solution, but not the entire solution
Cloud-based data recovery services are an excellent option for small businesses that need to recover lost or corrupted files quickly and easily. But when it comes to protecting your company against cyberattacks like ransomware or phishing scams, the cloud can only do so much — businesses still need to implement other strategies as well. As an example, consider an application that uses a database in the cloud and writes data back to that same database. In this scenario, if there were an attack on either of those two endpoints — the app or its connection with its database — a company could be left without access to all of its data until someone manually restores them from backups or otherwise fixes things up again after an incident has been resolved.
Infrastructure security
Infrastructure security is one of the major concerns when it comes to data sharing. For this reason, multiple approaches, tools, and solutions are included in business continuity planning and disaster recovery strategies. There are requirements established at the level of an organization within a certain industry or nationwide.
The benefit of complying with standards and laws that aim at personal data security is that you can meet the requirements of your industry or the regulations of your country. This will help you achieve your business objectives. However, compliance alone is not enough to protect a business against disasters and unplanned outages. A good disaster recovery plan should include additional measures such as regular testing and exercising of backups, as well as periodic training for staff members on how to respond if an outage occurs (or has already occurred). This is where cloud solutions come in handy in case of issues with access to the physical data stored in offices of archives, for instance. Most cloud solutions for data management and storage today are handling data in compliance with the existing regulations, therefore access to these data is granted upon authorization, and can be extremely challenging to hack.
From the client’s perspective, businesses and service providers that stick with the regulations and standards help them build confidence toward partnering with them as well as prevent any cyber threats to their personal information, hence, will not harm the business operations of either party.
The importance of compliance with the regulations and requirements
By understanding the regulations and standards that apply to your industry, you can begin to evaluate the benefits of compliance and determine whether it is worth investing time, money, and resources into ensuring that your organization is compliant with these requirements.
The consequences of non-compliance are significant; failing to meet compliance requirements could result in fines or other penalties from regulators or even loss of license/permit/authority if applicable (e.g., being unable to sell products). In addition, non-compliant businesses may have difficulty attracting customers who may be uncomfortable doing business with an unregistered company or one that has been cited for poor practices related directly back to their supply chain/suppliers.
Compliance requirements are rules or standards that must be met to comply with a certain regulation or standard. The most common compliance requirements come from organizations, industries, and governments: HIPAA, SOC 2, PCI DSS, FISMA, and GDPR, to name a few.
Conclusion
The world of cyber security is rapidly changing, and it’s important to keep up with the latest trends. The key takeaway is that there is no single solution for data security and resilience. You need to consider all of these factors when building a more resilient application: cloud-based backup services, encryption software, or hardware solutions like SD cards or USB drives; even old-fashioned pen-and-paper backup systems can play an important role in keeping your data safe from loss or damage.
The compliance requirements for your business are determined by the industry in which it operates and the jurisdiction where it is located. For example, HIPAA compliance is required by law for healthcare organizations that manage protected health information (PHI), while SOX compliance applies to publicly traded companies. Some standards are specific to certain industries like PCI DSS or FISMA while others apply across all industries such as NIST 800-53 security controls
Follow Me

Unleashing the Power of the Office Accelerator: Maximizing Productivity and Efficiency in the Workplace with Office 365 Accelerator

Unlocking the Hidden Potential of Your Website: Strategies for Growth

From AI to VR: How Cutting-Edge Tech Is Reshaping Personal Injury Law in Chicago
Trending
 Microsoft4 years ago
Microsoft4 years agoMicrosoft Office 2016 Torrent With Product Keys (Free Download)
 Torrent4 years ago
Torrent4 years agoLes 15 Meilleurs Sites De Téléchargement Direct De Films 2020

 Money4 years ago
Money4 years ago25 Ways To Make Money Online
 Torrent4 years ago
Torrent4 years agoFL Studio 12 Crack Télécharger la version complète fissurée 2020
 Education3 years ago
Education3 years agoSignificado Dos Emojis Usado no WhatsApp

 Technology4 years ago
Technology4 years agoAvantages d’acheter FL Studio 12

 Technology4 years ago
Technology4 years agoDESKRIPSI DAN MANFAAT KURSUS PELATIHAN COREL DRAW
 Education3 years ago
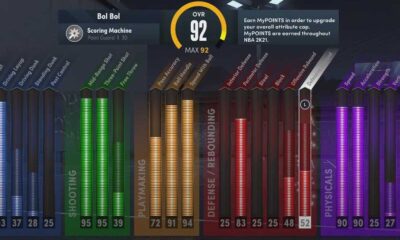
Education3 years agoBest Steph Curry NBA 2K21 Build – How To Make Attribute, Badges and Animation On Steph Curry Build 2K21

You must be logged in to post a comment Login